Modern IT teams face mounting challenges in keeping networks efficient, secure, and compliant. As infrastructure becomes more complex, it’s paramount to have effective strategies in place to manage network assets. Leveraging the right network inventory management software enables organizations to gain real-time visibility and confidence in their technology stack. This foundational step not only helps protect sensitive data but also streamlines routine tasks, freeing teams to focus on innovation.
Automated asset discovery, robust audit controls, and centralized repositories make it easier to respond to cyber threats and regulatory changes. Integrating inventory processes with wider IT service management operations can reduce costs and expedite incident responses. The following key steps, informed by industry best practices, will help IT leaders maintain a holistic, proactive approach to network inventory management.
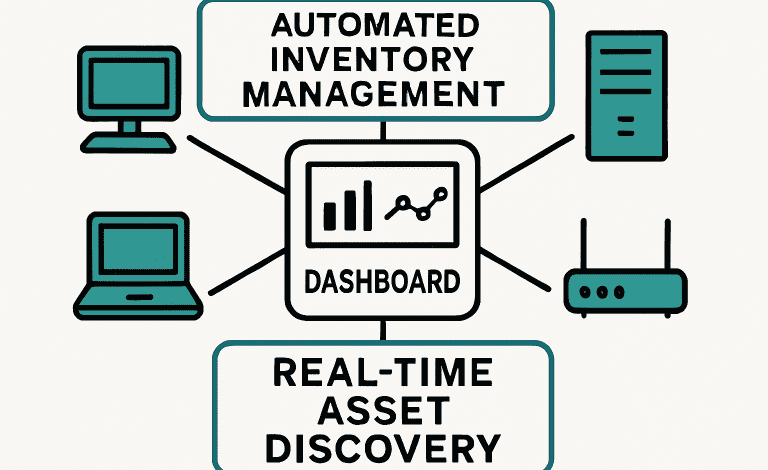
Automate Asset Discovery
Manual device tracking is time-consuming and often results in overlooked assets and outdated records. By implementing automated discovery tools, IT teams can instantly and accurately detect every device connecting to the network. Automated platforms map assets in real-time and update the inventory as soon as new endpoints come online. This is crucial for minimizing security risks and reducing the prevalence of “shadow IT” devices, which often introduce vulnerabilities. Modern discovery tools not only boost staff productivity but also form the backbone of reliable network management strategies.
Conduct Regular Audits
Maintaining a robust network inventory is only possible with scheduled, systematic audits. Reviewing inventory monthly or quarterly helps uncover discrepancies, unauthorized devices, and out-of-date records. Audits are also vital for regulatory compliance, providing documentation required during IT inspections or external reviews. During an audit, teams should verify the physical presence and operational status of each device, and update records to reflect any decommissioned or modified equipment. Consistent audit cycles not only support compliance but also optimize lifecycle management by identifying underused or obsolete assets that can be safely reallocated or retired.
Integrate with IT Service Management Tools
Integrating network inventory data with IT Service Management (ITSM) solutions streamlines incident handling and change management. When ticketing and inventory systems communicate seamlessly, technicians have immediate access to up-to-date device information, facilitating swift resolution. For example, if a service desk ticket is triggered for a malfunctioning asset, integrated systems can automatically retrieve hardware history, configuration data, and previous incident reports. This link between inventory and incident management reduces response time and ensures maintenance actions are accurate, minimizing disruption and downtime across the business.
Implement Real-Time Monitoring and Alerts
Continuous asset monitoring provides a first line of defense against unauthorized access and performance degradation. Real-time monitoring solutions flag suspicious activities, hardware failures, or emerging vulnerabilities the moment they occur, sending immediate alerts so issues can be addressed before they impact operations. Such technologies don’t just reduce threats; they support network optimization by highlighting bottlenecks, system faults, and resource constraints. For a deeper dive into continuous monitoring practices, check trusted publications like TechTarget for industry analysis and case studies.
Centralize Data Repositories
Consolidating network asset data into a single, centralized repository fosters better decision-making and more strategic infrastructure management. Centralized records provide a consistent view of hardware and software assets, improving the accuracy of reporting, budgeting, and capacity planning. Unified platforms can pull data from diverse sources, such as automated discovery tools, ITSM, and security solutions—ensuring that the entire IT estate is visible and accounted for. This not only reduces duplication and manual reconciliation but also equips leaders with up-to-date insights needed to plan for organizational growth and digital transformation.
Leverage Automation for Routine Tasks
Many tasks involved in inventory management, such as software patching, compliance checks, and documentation, are ripe for automation. By offloading these repetitive processes, IT teams reduce the likelihood of errors and free up time for higher-value work. Automated patch management, for example, ensures that all endpoints are consistently updated against the latest security threats, minimizing risk without additional overhead. Scripting compliance checks to run on schedule helps organizations stay audit-ready year-round, reducing manual effort and ensuring that every device remains in compliance with prescribed policy guidelines.
Enhance Security and Compliance
Detailed, up-to-date inventories play a pivotal role in reducing risk and ensuring regulatory compliance. With complete visibility, teams can quickly identify outdated, unpatched, or unauthorized equipment. This makes it easier to spot exposure points and act decisively—whether through isolation, patching, or decommissioning. Documentation generated by robust inventory platforms also streamlines compliance, making audits for standards such as GDPR, PCI-DSS, and SOX far less burdensome. According to Fortinet, asset awareness forms the foundation of enterprise cybersecurity, underpinning the most effective defense frameworks.
Final Thoughts
Mastering network inventory management lays the groundwork for secure, efficient, and scalable IT operations. By automating asset discovery, conducting regular audits, integrating with ITSM tools, and centralizing data, organizations drive operational excellence and reinforce their security and compliance postures. These actions not only protect valuable technology investments but also position teams for success in a rapidly changing digital world.